A new information-stealing malware called Mystic Stealer has been found to steal data from about 40 different web browsers and over 70 web browser extensions.
First advertised on April 25, 2023, for $150 per month, the malware also targets cryptocurrency wallets, Steam, and Telegram, and employs extensive mechanisms to resist analysis.
“The code is heavily obfuscated making use of polymorphic string obfuscation, hash-based import resolution, and runtime calculation of constants,” InQuest and Zscaler researchers said in an analysis published last week.
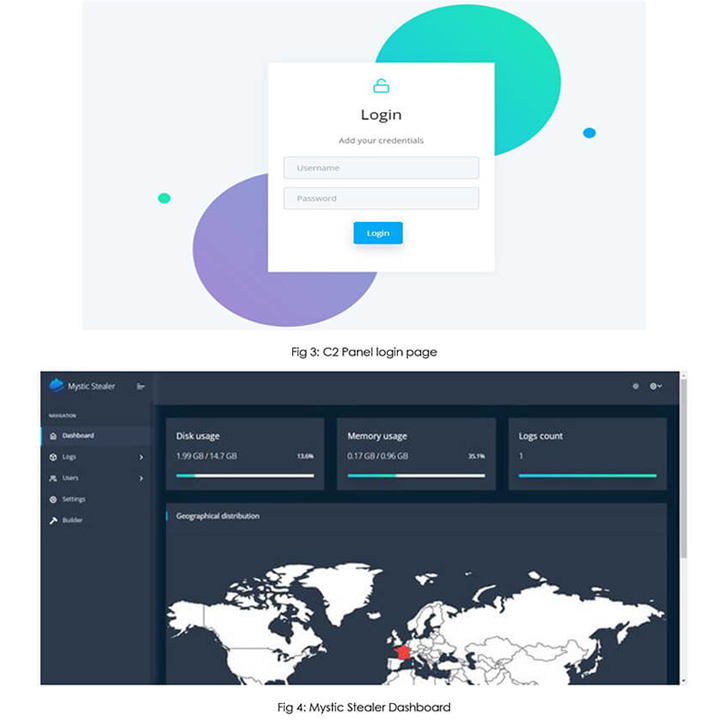
Mystic Stealer, like many other crimeware solutions that are offered for sale, focuses on pilfering data and is implemented in the C programming language. The control panel has been developed using Python.
Updates to the malware in May 2023 incorporate a loader component that allows it to retrieve and execute next-stage payloads fetched from a command-and-control (C2) server, making it a more formidable threat.
C2 communications are achieved using a custom binary protocol over TCP. As many as 50 operational C2 servers have been identified to date. The control panel, for its part, serves as the interface for buyers of the stealer to access data logs and other configurations.
Cybersecurity firm Cyfirma, which published a concurrent analysis of Mystic, said, “the author of the product openly invites suggestions for additional improvements in the stealer” through a dedicated Telegram channel, indicating active efforts to court the cybercriminal community.
“It seems clear that the developer of Mystic Stealer is looking to produce a stealer on par with the current trends of the malware space while attempting to focus on anti-analysis and defense evasion,” the researchers said.
The findings come as infostealers have emerged as a hot commodity in the underground economy, often serving as the precursor by facilitating the collection of credentials to enable initial access into target environments.
Put differently, stealers are used as a foundation by other cybercriminals to launch financially motivated campaigns that employ ransomware and data extortion elements.
The spike in popularity notwithstanding, off-the-shelf stealer malware are not only being marketed at affordable prices to appeal to a wider audience, they are also evolving to become more lethal, packing in advanced techniques to fly under the radar.
The ever-evolving and volatile nature of the stealer universe is best exemplified by the steady introduction of new strains such as Album Stealer, Aurora Stealer, Bandit Stealer, Devopt, Fractureiser, and Rhadamanthys in recent months.
In a further sign of threat actor’s attempts to evade detection, information stealers and remote access trojans have been observed packaged within crypters like AceCryptor, ScrubCrypt (aka BatCloak), and Snip3.
The development also comes as HP Wolf Security detailed a March 2023 ChromeLoader campaign codenamed Shampoo that’s engineered to install a malicious extension in Google Chrome and steal sensitive data, redirect searches, and inject ads into a victim’s browser session.
Transform Your Risk Management: The Ultimate Guide to Modern Exposure Management
Don’t risk your organization’s security. Download our whitepaper on establishing a Modern Exposure Management Program for accurate risk assessment.Download Guide
“Users encountered the malware mainly from downloading illegal content, such as movies (Cocaine Bear.vbs), video games, or other,” security researcher Jack Royer said. “These websites trick victims into running a malicious VBScript on their PCs that triggers the infection chain.”
The VBScript then proceeds to launch PowerShell code capable of terminating all existing Chrome windows and opening a new session with the unpacked rogue extension using the “–load-extension” command line argument.
It also follows the discovery of a new modular malware trojan christened Pikabot that has the ability to execute arbitrary commands and inject payloads that are provided by a C2 server, such as Cobalt Strike.
The implant, active since early 2023, has been found to share resemblances with QBot with regard to distribution methods, campaigns, and malware behaviors, although there is no conclusive evidence connecting the two families.
“Pikabot is a new malware family that implements an extensive set of anti-analysis techniques and offers common backdoor capabilities to load shellcode and execute arbitrary second-stage binaries,” Zscaler said.