As many as five security flaws have been disclosed in Netgear RAX30 routers that could be chained to bypass authentication and achieve remote code execution.
“Successful exploits could allow attackers to monitor users’ internet activity, hijack internet connections, and redirect traffic to malicious websites or inject malware into network traffic,” Claroty security researcher Uri Katz said in a report.
Additionally, a network-adjacent threat actor could also weaponize the flaws to access and control networked smart devices like security cameras, thermostats, smart locks; tamper with router settings, and even use a compromised network to launch attacks against other devices or networks.
The list of flaws, which were demonstrated at the Pwn2Own hacking competition held at Toronto in December 2022, is as follows –
- CVE-2023-27357 (CVSS score: 6.5) – Missing Authentication Information Disclosure Vulnerability
- CVE-2023-27368 (CVSS score: 8.8) – Stack-based Buffer Overflow Authentication Bypass Vulnerability
- CVE-2023-27369 (CVSS score: 8.8) – Stack-based Buffer Overflow Authentication Bypass Vulnerability
- CVE-2023-27370 (CVSS score: 5.7) – Device Configuration Cleartext Storage Information Disclosure Vulnerability
- CVE-2023-27367 (CVSS score: 8.0) – Command Injection Remote Code Execution Vulnerability
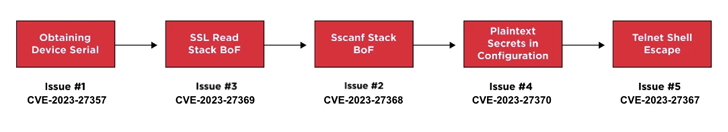
A proof-of-concept (PoC) exploit chain illustrated by the industrial cybersecurity firm shows that it’s possible to string the flaws — CVE-2023-27357, CVE-2023-27369, CVE-2023-27368, CVE-2023-27370, and CVE-2023-27367 (in that order) — to extract the device serial number and ultimately obtain root access to it.
“These five CVEs can be chained together to compromise affected RAX30 routers, the most severe of which enable pre-authentication remote code execution on the device,” Katz noted.
Users of Netgear RAX30 routers are advised to update to firmware version 1.0.10.94 released by the networking company on April 7, 2023, to address the flaws and mitigate potential risks.